THE INFORMATION IN THIS ARTICLE APPLIES TO:
- EFT Server, version 6.4 - 7.3.3.20
SYMPTOM
Java Security Warning prompt appears while the Web Transfer Client (WTC) or the Secure Ad Hoc Transfer (SAT) module is loading.
RESOLUTION
Upgrading from v6.4.x to v6.4.19 or from v6.5.x to v6.5.5.2 corrects the issue.
Alternatively, you can work around the issue until you are ready to upgrade by installing the attached JAR files as described below.
To work around the issue
- Back up the following SAT (if used) and WTC folders:
- SAT: C:\InetPub\wwwroot\EFTAdhoc\lib
- WTC: C:\Program Files (x86)\GlobalSCAPE\EFT Server Enterprise\web\public\EFTClient\wtc\lib
- Stop the EFT Server service and IIS.
- Extract the contents of the attached ZIP file.
- Copy the contents of the SAT folder in the ZIP file to C:\InetPub\wwwroot\EFTAdhoc\lib (if the SAT module is installed).
- Copy the contents of the WTC folder in the ZIP file to C:\Program Files (x86)\GlobalSCAPE\EFT Server Enterprise\web\public\EFTClient\wtc\lib.
- After overwriting the old files with the new files, start the EFT Server service and IIS.
- To verify whether the issue was corrected, clear the web browser cache, close and then reopen the browser, and then browse to the page as usual.
MORE INFORMATION
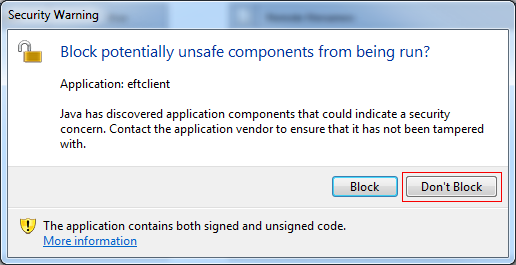
As of Java update 7u21, Java has started warning users of potentially unsafe code when web applications they are about to run contain JavaScript code that is used with trusted Java components. A dialog, shown above, gives the user the option to block the application or to keep going.
Java provides a mechanism for keeping the user from being prompted and it has been implemented for the WTC/SAT. However, until the fix has been propagated to EFT Server, there is a temporary workaround to avoid displaying the prompt every time the WTC/SAT is started. You can disable the prompt in the Java Control Panel.
To disable the prompt
- Click Start > Control Panel, then click the Java icon. (Or click Start > Run, type/paste: c:\Program Files (x86)\Java\jre6\bin\javacpl.exe, then click OK. This is the default path; your path may differ.)
- In the Java Control Panel, click the Advanced tab, and scroll toward the bottom of the dialog box.
- In the Mixed code area, click Enable - hide warning and run with protections.
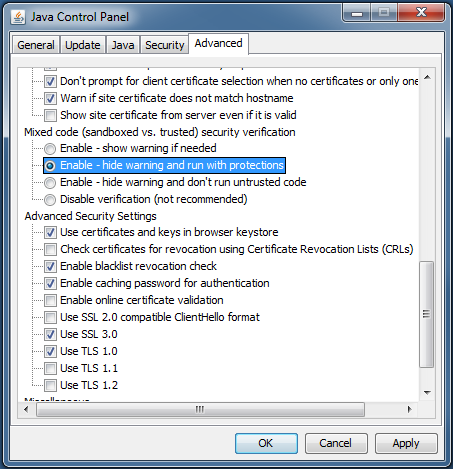
- Click OK.
This should be considered a temporary solution as hiding this prompt may allow malicious software to have access to the client and server systems.
For more information about the Mixed code options, refer to http://docs.oracle.com/javase/7/docs/technotes/guides/jweb/mixed_code.html#jcp