THE INFORMATION IN THIS ARTICLE APPLIES TO:
- EFT Enterprise, version 6.1 and later
DISCUSSION
EFT has several mechanisms in place for detecting attacks on the server. However, failed login attempts spaced out over a time are not handled automatically. The usual scenario is "script kiddies" attempting to log in using “root” or “administrator” with each login attempt spaced out over 5, 10, 15, or even 30 minutes so as to avoid the "build automatic ban" systems that are more geared towards large scale attacks mounted over a short time span. To address the problem, the server should ban the IP address of these users immediately following a failed login attempt that uses a reserved name (admin, administrator, sa, root, superuser, etc.).
The EFT Advanced Workflow Engine (AWE) and Event Rules coupled with the built in programmatic interface (COM API) can be leveraged to ban the IP address of users who attempt to log in using a reserved username (any username you define).
Use the procedure below to import the attached workflow and then create an Event Rule that uses the workflow. EFT will call the workflow for every FAILED login attempt, at which point the workflow tests the login name provided against the banned login name list that you create. If a match occurs, then the IP address of the user is added to EFT’s ban list for all Sites.
To create the ban script kiddies Event Rule
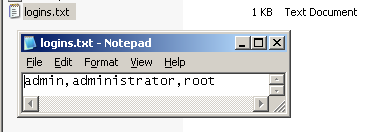
- Create a text file and type in the list of banned names in comma delimited format (e.g., administrator,root,admin).
- Save the text file as logins.txt in the root of the EFT computer's C drive. (If you use a different name or location, then be sure to edit the location in the workflow later.)
- Under "Attachments" below, download and save banscriptkiddies.txt (for EFT Versions prior to v7.4.7) or banscriptkiddies_For_AWE10.txt (for EFT v7.4.7 later) to the EFT computer, then rename it with the aml extension.
(It doesn't matter where you save it; you will import it to the AWE module next.)
- Open the EFT administration interface and log in.
- Click the Advanced Workflows node, and then in the right pane, click Import.
- In the Open dialog box, click banscriptkiddies.aml, and then click Open.
- In the Import Workflow dialog box, provide a name and (optional) description for the workflow, then click OK. The workflow appears in the Advanced Workflows node.
- In the right pane, click Edit to open the workflow in the Advanced Workflow Task Builder.
- Double-click each of the global variables to edit the EFT Server host, port, admin username, and admin password (workflow steps 3-6) and change them to your EFT host, username, password, and port.
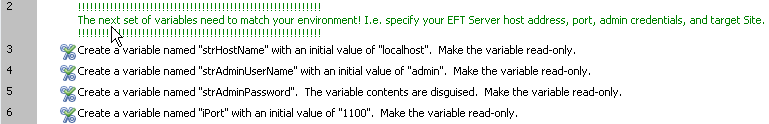
- If you used a different name or location for logins.txt, then edit the location in workflow step 16 also.

- Click Run to verify that you have provided the correct host, username, password, and port to connect to the server.
- Click Save and Close.
- Create a new “User Login Failed” Event Rule:
- Click to select the Event Rules node, then in the right pane, click New.
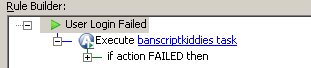
- In the Create New Event Rule dialog box, click User Login Failed, then click Create.
- In the Actions pane, double-click Execute Advanced Workflow to add the workflow to the rule.
- In the Rule Builder, click the Action to open the Advanced Workflow dialog box.
- In the Choose a workflow to execute box, specify the banscriptkiddies workflow, and then click OK.
- Click Apply to save the Event Rule.
- Test the Event Rule by attempting to login from another system using a banned username from your logins.txt file.
- Refresh EFT Server’s interface, and then check the IP access/ban list for the banned IP addresses (Site > Connections > IP access/ban list).
- Be sure to remove from the IP Auto-ban dialog box the banned IPs that were added from your testing.